White-box cryptography
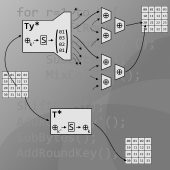
I did a 10 weeks internship project at UL-TS on the subject of white-box cryptography. While modern encryption algorithms are designed to work in a black-box context, where an attacker can only play with inputs and outputs, white-box cryptography aims to implement these algorithms in such a way that they are safe in a white-box context, where an attacker can read and alter each step of the execution. The current way to do so (for block ciphers) is to implement it as a network of encoded lookup tables.
During the internship I created a white-box implementation of AES, which I present here as
a challenge. The goal is to recover the key bytes, goodluck!
For hints or spoilers you can have a look at my internship report. Section 2 describes the
technical details of the implementation and section 4 might contain some helpful ideas on
how to break the white-box.
Download the challenge or read my report.
More info
Two really good articles about white-box cryptography are the tutorial on a white-box AES
implementation by James Muir
(pdf,
google scholar)
and the article by Rod Schultz on the practical side of obfuscation and white-box
cryptography in DRM applications
(pdf,
google scholar).
I can also recommend the website of Brecht Wyseur:
whiteboxcrypto.com.
